On September 8th, the Node.js ecosystem was hit by one of the most widespread supply chain attacks ever reported. A malicious actor poisoned numerous npm packages, compromising thousands of developers and organizations. This incident is another stark reminder: your software supply chain is only as secure as its weakest dependency. Why This Matters Modern applications…
Continue ReadingOpen Source Software
Industry News
Fidelity says data breach exposed personal data of 77,000 customers
Internet Archive hacked, data breach impacts 31 million users
Water supplier American Water Works says systems hacked
Attackers Flood NPM Repository with Over 15,000 Spam Packages Containing Phishing Links
SEC Charges SolarWinds and CISO with Fraud, Internal Control Failures
How to Manage Open Source Software Vulnerabilities Without Slowing Your Team Down
Open source software is a critical component of modern applications, but it also introduces security risks that must be managed effectively. For Software Engineering and Information Security Managers, balancing vulnerability remediation with development speed can be challenging, especially when adopting new security tools. While the initial learning curve may seem steep, refining software development processes…
Continue ReadingGetting the Most Out of SCA
Software Composition Analysis (SCA) is an important practice in modern software development, enabling teams to manage and secure the open-source components within their applications. By effectively utilizing SCA tools, such as SOOS’s Software Composition Analysis, you can identify vulnerabilities, ensure license compliance, and maintain the integrity of your software to avoid costly security, business, and…
Continue ReadingTips to Easily Compare Open Source Software Licenses and Protect Your Business
Open source software (OSS) powers much of the technology we rely on today, speeding the pace of innovation and enabling unprecedented collaboration on new product development. And one of the most important and often overlooked aspects of open source software is knowing what software you can legally use, in which situations, and with what requirements….
Continue ReadingSOOS Community Edition is Totally Free!
SOOS’s new Community Edition is a totally free version of our software composition analysis (SCA) tool available to educational users and all developers working on open source projects. That’s FREE, as in beer. Free Vulnerability Scanner Now you can access the most practical and effective supply chain security tool available, at no cost. Identify and…
Continue ReadingSOOS Year in Review
We’ve had an exciting year at SOOS. We want to thank all of our customers for a great 2022, and an even better 2023!
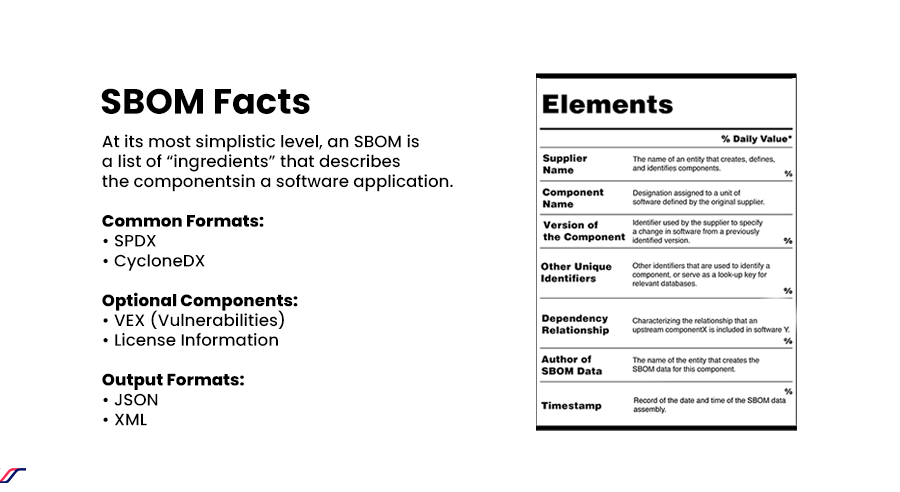
Continue ReadingSBOM 101: What is an SBOM? Why are they important?
SBOM stands for “software bill of materials.” At its most simplistic level, an SBOM is a list of “ingredients” that describes the components in a software application. More precisely (per the NTIA), a SBOM is a “complete, formally structured list of components, libraries and modules that are required to build a given piece of software…
Continue ReadingSoftware License Management Basics
Companies that use multiple software packages may not be using them to their full potential. Others might have expired licenses in their inventory. Both situations can cost money. Software license management procedures help businesses stay up to date with everything related to software licenses. SOOS wants you to understand the importance of software licensing as it…
Continue ReadingSoftware Industry Total Cost of Ownership
ROI is a primary concern for any enterprise undertaking, and enterprise software projects are no different. The total cost of ownership is a valuable input to an accurate ROI projection. Unfortunately, many businesses and IT leaders don’t take all the costs of the different options the software industry offers into consideration. Those oversights can lead…
Continue ReadingSoftware Security Audit Guide for Software Acquisition
Mergers and acquisitions are standard business practices; they allow companies to grow and obtain assets to increase competitiveness and their bottom line. However, while these contractual allegiances and alliances are primarily bureaucratic, the evolution of technology created addendums to standard protocols, including a software security audit. The evolution of technology and the dependence on software is…
Continue Reading