FDA-Ready SBOMs Built Into Your SDLC
SOOS is the SBOM-First ASPM for medical devices. Generate, validate, and defend SBOMs, prove your vulnerability plan, and ship §524B-ready submissions without delaying release.
Get Your FDA-Ready SBOM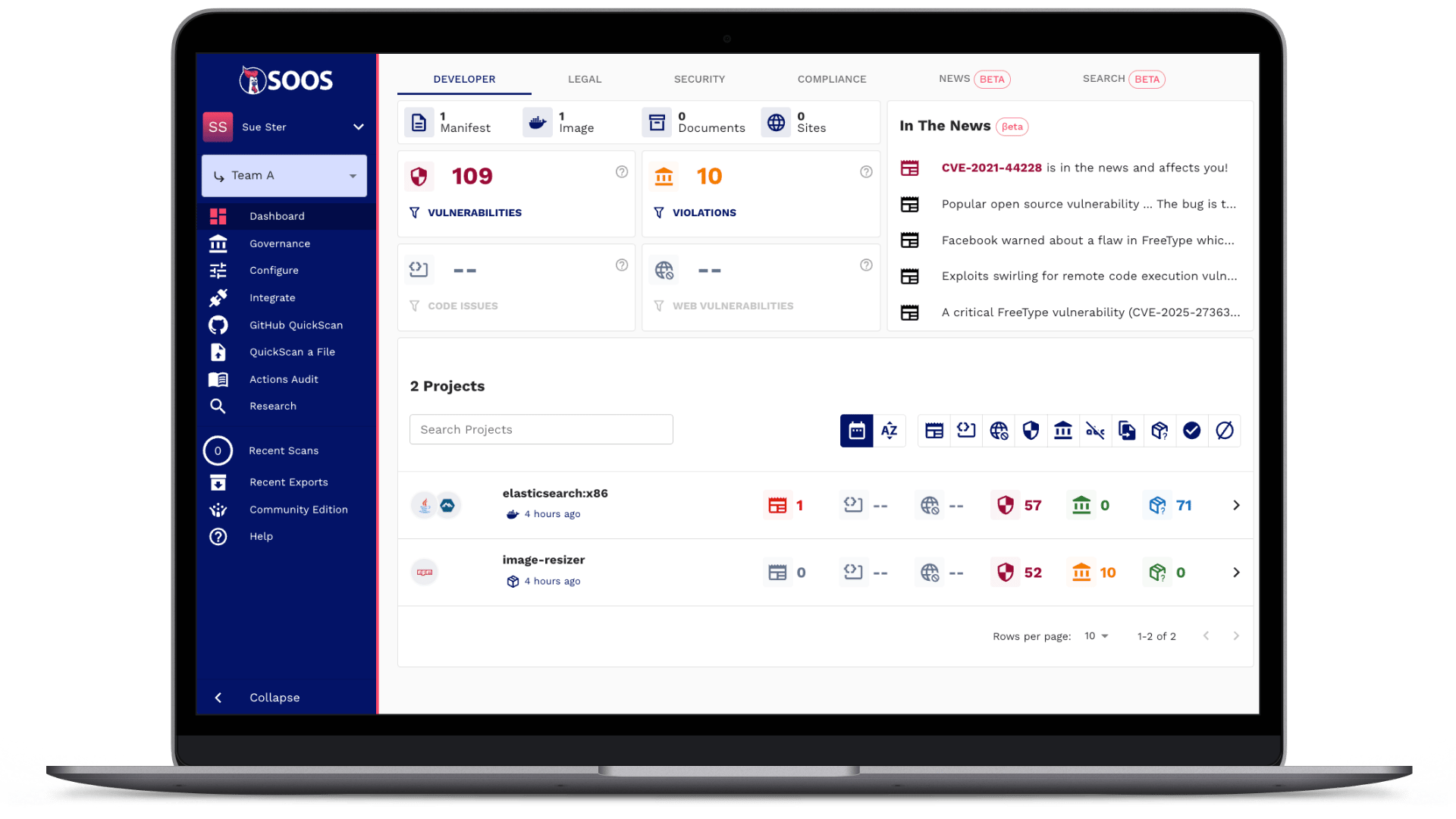
AppSec Meets Submission Readiness
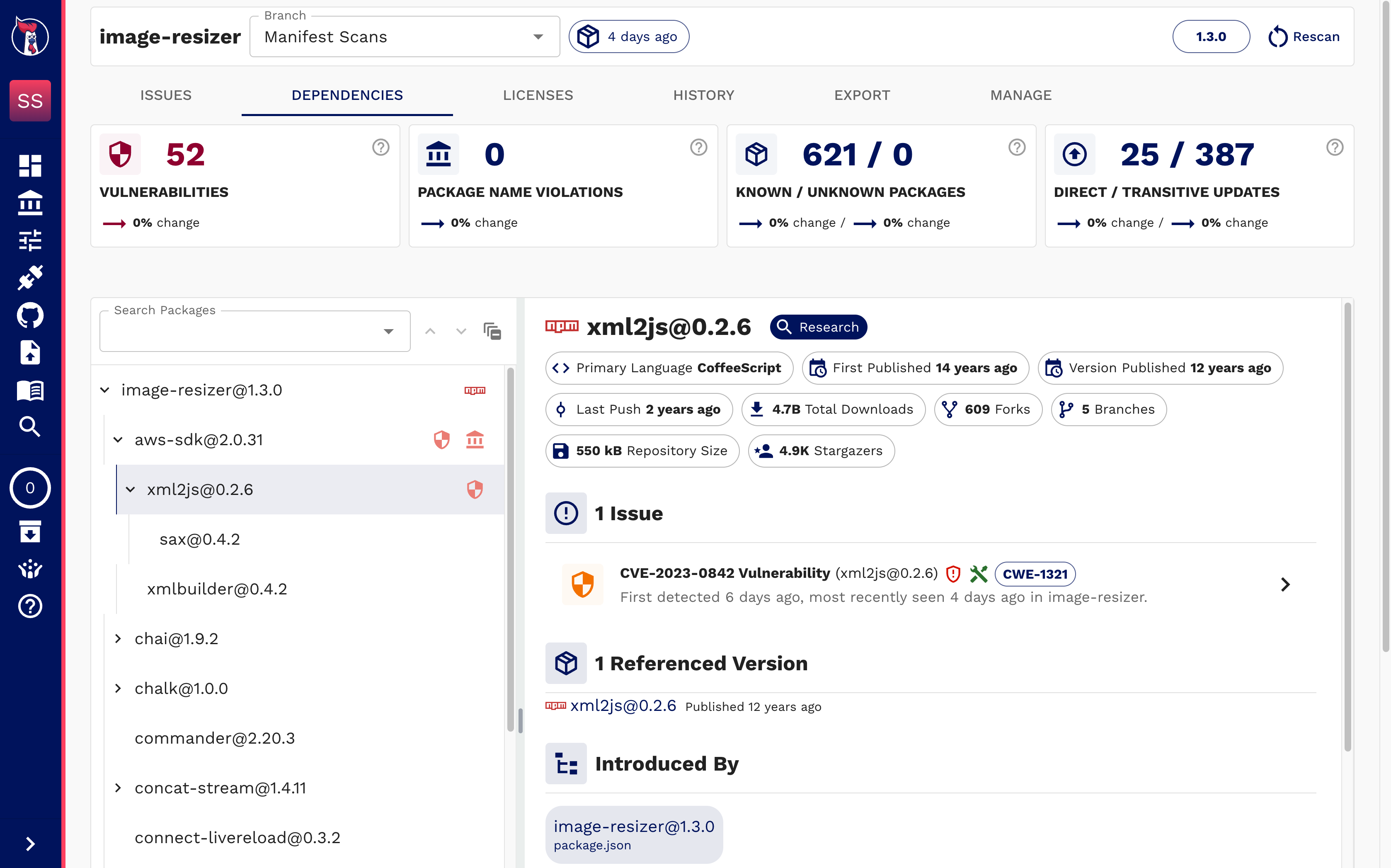
SOOS manages your SBOMs, scans, and SLAs in one view: fields are validated, vulnerabilities are prioritized, VEX/attestations are tracked and timestamped—so teams fix faster and reviewers get defensible evidence.
Security without slowdown — SBOM-First ASPM ships FDA-ready evidence
Defend Your Inventory
Continuously inventory components across source, containers, and ingested SBOMs. Consolidate many SBOMs into one linked archive.
Works Where You Build
Run in CI/CD, scan repos, images, binaries, or ingest third-party SBOMs. Cross-convert SPDX ↔ CycloneDX, no rebuilds required.
Emerging Threats
SOOS tracks new CVEs and industry headlines against your dependency tree. We flag past headliners (Log4Shell, xz, etc) and show fix guidance so you can act before it hits review.
Guided Upgrade Paths
Get fix versions and upgrade paths—even when findings originated from an ingested SBOM or binary, not your source.
FDA-Ready Fields
Generate FDA-compliant SBOMs with required fields, including end-of-life/service dates.

SLA-Driven Remediation
SLAs and a Compliance dashboard surface approaching/overdue items so you can prove timely handling.
Postmarket Plan, Proven
Show intake→triage→remediation history with timestamps. Automate evidence collection for your §524B(b)(1) plan.

All Formats Welcome
Bring SPDX, CycloneDX, or CSVs. SOOS normalizes, enriches, and cross-converts, consolidates into a linked archive, and exports submission-ready SBOMs.

VEX Cuts False Urgency
Publish CSAF VEX or CycloneDX attestations and re-score vulns so reviewers see real risk, not noise.
Want to see an FDA-ready SBOM from SOOS?
Download a sample CycloneDX SBOM showing a VEX attestation and rescored vulnerability.
Sign-up for a free trial
to work with all of SOOS's powerful report formats, including CycloneDX and SPDX Software Bill of Materials (SBOMs), standalone CSAF VEX, SARIF results, open source license reports, and more.
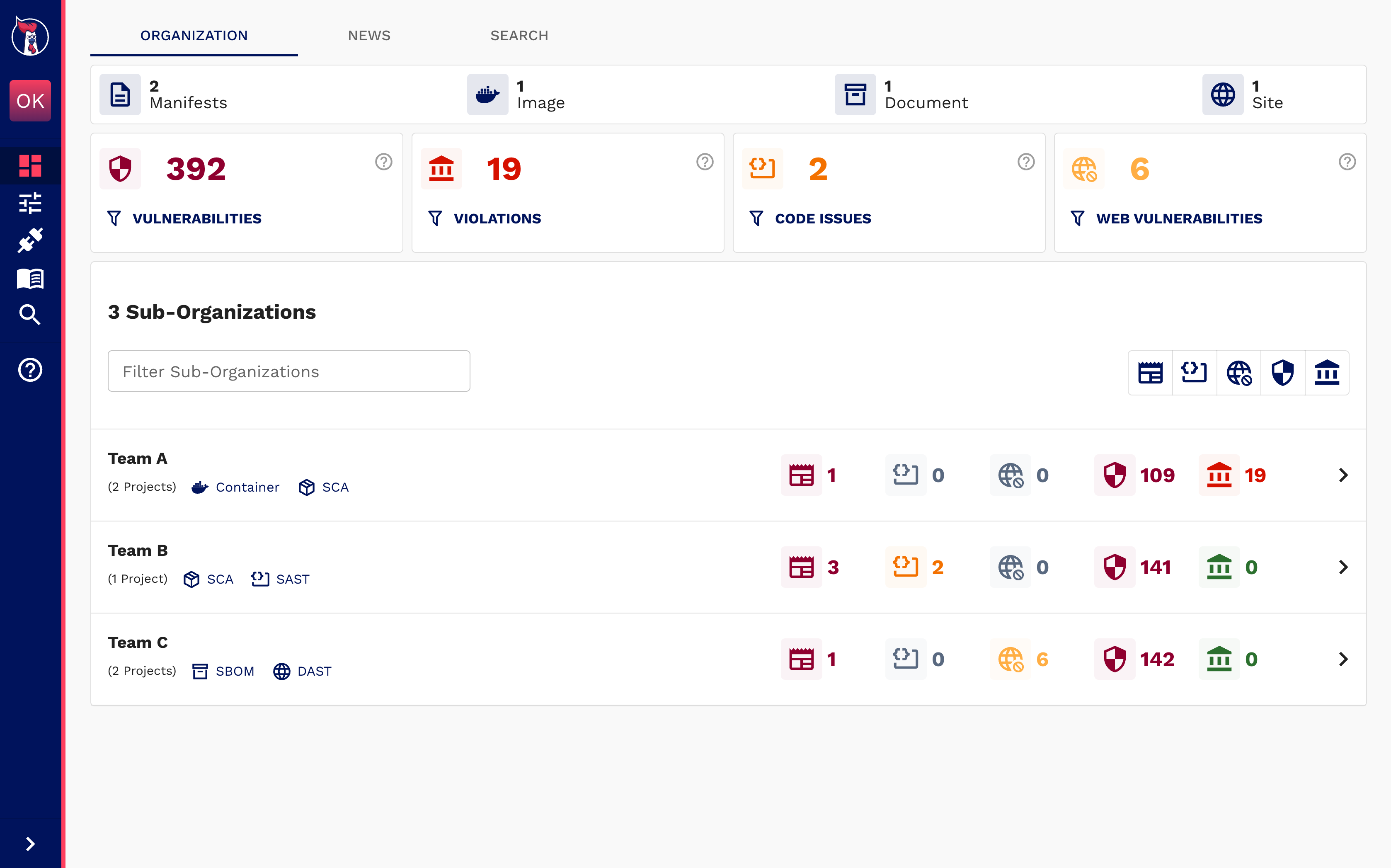
AppSec Meets Submission Readiness
Track inventory, vulnerabilities, SLAs, and change history in a single dashboard. Generate an FDA compliant SBOM any time and attach it to your premarket file.
White-Glove Help, Fast Turnaround
We’ll stand up your first FDA-ready SBOM from repos, containers, filesystem scans, or even existing SBOMs, then automate it in your pipeline. Most teams export compliant SBOMs the same day.
Automate Your Software Inventory
Start from what’s real: your components. SOOS ingests software artifacts like manifests, SBOMs, scans binaries/containers, and continuously maintains a consolidated, linked SBOM archive you can defend.
Frequently Asked Questions
What is SBOM-First ASPM?
Application Security Posture Management (ASPM) is how you continuously understand, prioritize, and fix risk across all the software you build, buy, and run. SBOM-First ASPM means you treat the bill of materials (and everything that enriches it) as the living source of truth throughout the SDLC, and not as a static document you file away.
How is SOOS different from typical med-device SBOM tools?
Most “SBOM vaults” in the medical device world are document stores: you upload/import SBOMs, maybe edit, and export reports for submissions. Useful, but static. SOOS is built to operate those artifacts across engineering workflows.
What does §524B actually require?
For cyber devices, the FDA expects your premarket submission to demonstrate: (1) a plan to monitor and address postmarket vulnerabilities, (2) processes to assure cybersecurity and provide updates/patches, and (3) inclusion of SBOM(s) in the file.
Does SOOS produce FDA-ready SBOMs?
Yes. We generate/validate SPDX and CycloneDX, populate FDA-expected fields (including EOL/EOS when available), and export attachable SBOMs.
Can we include VEX/attestations with our submission?
Yes. Output CSAF VEX or CycloneDX attestations, plus vulnerability re-scoring to clarify actual exploitability/context.
How do you handle third-party SBOMs and binaries?
Ingest SPDX/CycloneDX, scan binaries/containers, enrich with SOOS data, and consolidate into one linked archive (bom-refs preserved).
Will this help with postmarket expectations?
Yes. SLAs, triage workflows, and remediation history form evidence for your postmarket vulnerability plan and ongoing monitoring. You can even generate an SBOM from any scan you've done in the last year, providing an easy way to show differences over time.

